Introduction
Open source software is usually associated with transparency, collaboration, and innovation. But there’s a darker side that many people don’t talk about enough: open source malware. In reality, not all malicious code is hidden behind closed doors—some of it is freely available, documented, and actively shared online.
For developers, security researchers, and even curious learners, this creates a confusing gray area. Is open code always safe? Or can openness actually make attacks easier? The truth sits somewhere in the middle, and understanding it matters more than ever.
As cyberattacks become more sophisticated, attackers are no longer reinventing the wheel. They reuse, modify, and improve existing code. That’s where this topic becomes critical for businesses, IT teams, and anyone responsible for digital systems today.
What Is Open Source Malware?
Open source malware refers to malicious software whose source code is publicly available. Anyone can view it, download it, modify it, or reuse it. Unlike traditional malware that is tightly guarded by cybercriminal groups, this code often lives on public repositories, forums, or research platforms.
The idea sounds contradictory at first. Malware is supposed to be secret, right? However, openness doesn’t remove its malicious intent. Instead, it lowers the barrier to entry, allowing attackers with limited skills to deploy effective threats.
It’s important to clarify one thing early: not every open malware project is created with criminal intent. Some are developed for education, testing defenses, or academic research. The danger begins when these tools escape controlled environments.

How Open Source Malware Actually Works
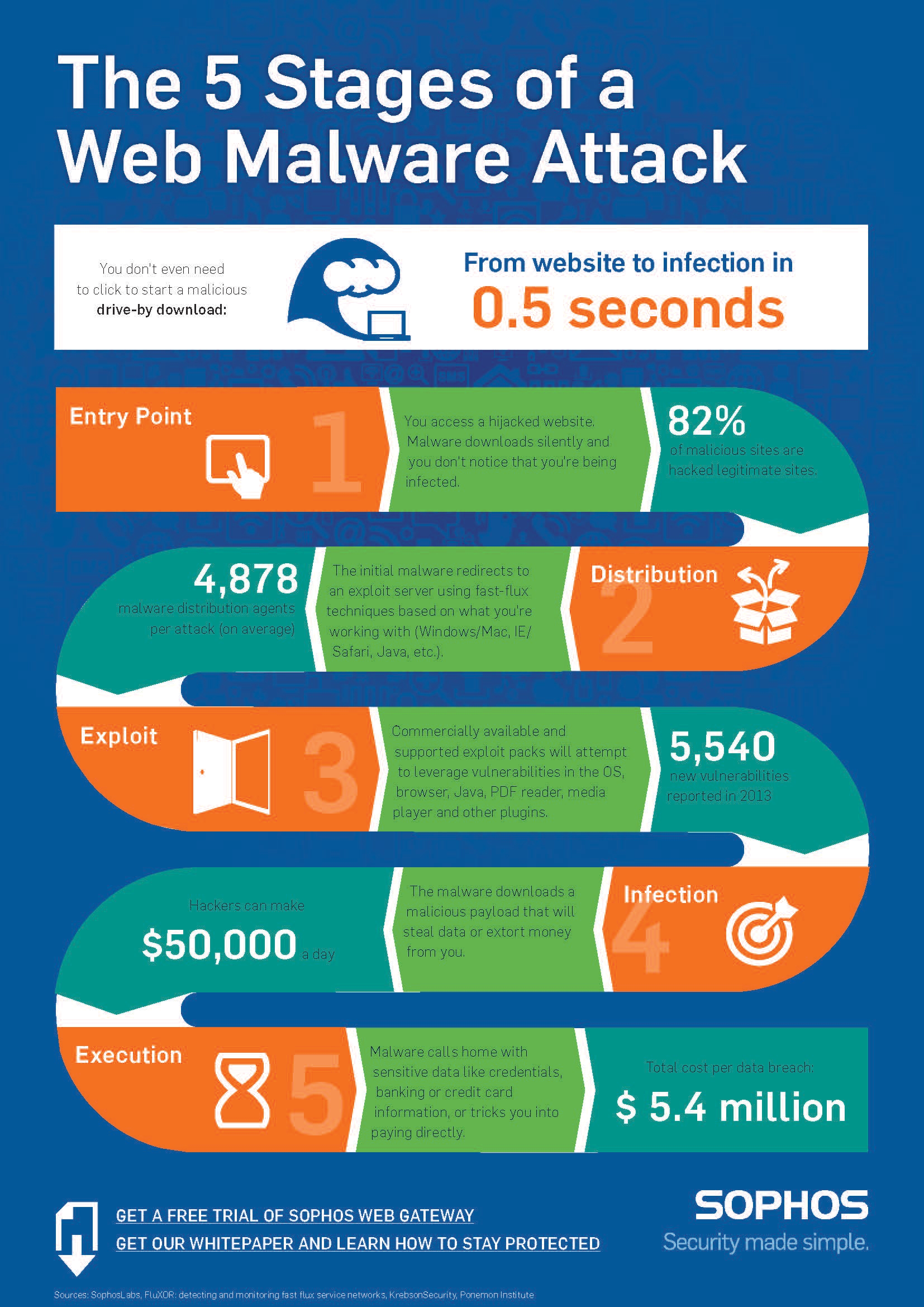
At a technical level, open source malware functions like any other malicious program. The difference lies in visibility. Because the code is open, attackers can quickly adapt it to new targets or bypass detection mechanisms.
Most projects include modular designs. One module might handle persistence, another communication with command-and-control servers, and another data exfiltration. This modularity makes customization frighteningly easy.
From a defender’s perspective, openness is a double-edged sword. Analysts can inspect the code and build signatures, but attackers can just as easily tweak it to evade those same defenses.
Why Attackers Use Open Source Malware
The appeal is simple: speed, cost, and efficiency. Writing sophisticated malware from scratch takes time and expertise. Using open projects cuts development cycles dramatically.
Another reason is community-driven improvement. Just like legitimate open software, malicious projects evolve. Bugs are fixed, features are added, and performance improves over time.
Finally, attribution becomes harder. When thousands of people use similar codebases, tracing an attack back to a specific actor becomes significantly more complex.
Common Types of Open Source Malware
Open source malware spans almost every category of digital threat. Below are some of the most common forms seen in the wild.
Remote Access Trojans (RATs)
These allow attackers to remotely control infected machines. Many open projects provide full-featured dashboards, making them attractive to novice attackers.
Keyloggers
Simple yet effective, keyloggers record user input. Open versions are often used as learning tools but can easily be weaponized.
Botnets
Open frameworks enable attackers to create networks of compromised devices. These botnets are often used for DDoS attacks or spam campaigns.
Ransomware Proof-of-Concepts
Some open projects claim to be educational demonstrations. Unfortunately, minor changes can turn them into real-world extortion tools.

Legitimate Uses vs Malicious Abuse
This is where nuance matters. Not all open malware code is inherently bad. Security professionals use it to test defenses, train analysts, and simulate attacks.
For example, penetration testers rely on known malicious frameworks to evaluate how well an organization detects threats. Universities use them to teach malware analysis safely.
The ethical line is crossed when such tools are deployed without consent or safeguards. Intent, context, and usage make all the difference.
Real-World Examples and Case Studies
Several high-profile incidents have involved modified open code. Attackers often start with publicly available projects and add custom features tailored to specific targets.
In one documented case, a small business network was compromised using a slightly altered open-source RAT. Antivirus tools failed to detect it because the signature no longer matched known samples.
These incidents highlight a key lesson: familiarity with open code does not guarantee immunity. Continuous monitoring and behavioral analysis remain essential.
Risks and Ethical Concerns
The biggest risk of open source malware is accessibility. When dangerous tools are easy to obtain, misuse becomes inevitable.
There’s also the ethical dilemma faced by developers. Should potentially harmful code be published at all? Some argue that transparency strengthens defenses, while others believe it fuels cybercrime.
Regulation remains inconsistent globally, leaving responsibility largely in the hands of the cybersecurity community.
How Security Teams Defend Against Open Source Malware
Defending against open threats requires a layered approach. Signature-based detection alone is not enough.
Behavioral Analysis
Instead of looking at code fingerprints, systems monitor suspicious actions like unusual network connections or privilege escalation attempts.
Threat Intelligence
Tracking known projects and their variants helps teams anticipate new attack patterns before they spread widely.
Regular Patching and Hardening
Many attacks succeed simply because systems are outdated. Closing these gaps dramatically reduces risk.
Security Awareness Training
Human error remains a major factor. Educated users are less likely to fall for phishing or social engineering tactics that deliver malware.
The Future of Open Source Malware
Looking ahead, the line between research tools and weaponized code will continue to blur. Artificial intelligence may accelerate both attack development and defense strategies.
We’re also likely to see more collaboration among attackers, borrowing practices from legitimate software communities. That said, defenders are adapting just as quickly.
Ultimately, understanding this landscape is no longer optional. Awareness is becoming a core component of digital resilience.
FAQs
What does open source malware mean?
Open source malware is malicious software whose source code is publicly available for anyone to view, modify, or reuse.
Is open source malware legal?
The code itself may be legal to publish, but using it to attack systems without permission is illegal in most countries.
Why would developers publish malware code openly?
Some do it for education, research, or testing security defenses. The problem arises when the code is misused.
Can antivirus software detect open source malware?
Sometimes, but modified versions can evade traditional signature-based detection.
Is open source malware more dangerous than closed malware?
Not necessarily more dangerous, but it is more accessible, which increases the likelihood of misuse.
How can businesses protect themselves?
By combining behavioral monitoring, threat intelligence, regular updates, and employee training.
Does open source malware help security research?
Yes, when used responsibly. It allows researchers to study real attack techniques in controlled environments.
Will open source malware increase in the future?
Most experts believe it will, as collaboration and code sharing continue to grow in both legitimate and malicious communities.
Conclusion
Open source malware challenges many assumptions about security, transparency, and trust in modern software. While openness can empower defenders, it also lowers the barrier for attackers who know how to exploit it. The real risk lies not in the code itself, but in how it’s used. By understanding how these tools work, why they exist, and how they’re abused, individuals and organizations can move from fear to informed defense. In today’s threat landscape, knowledge isn’t just power—it’s protection.